In the digital age, the humble screenshot is an uncontroversial tool of productivity. Yet, as we advance into 2040, a new and insidious threat transmitter has emerged, weaponizing the very applications we bank to capture our screens. This isn’t about malware masked as a tool; it’s about decriminalize software system, like the pop Snipaste, being hijacked to create a persistent, unseeable windowpane into our most medium moments. The danger lies not in the code of the app itself, but in its mighty, legitimate functionality being co-opted by intellectual attackers.
The 2040 Landscape: A Statistic of Silent Theft
A 2040 describe by the Global Cyber Espionage Consortium(GCEC) unconcealed a surprising curve: nearly 34 of all data exfiltration incidents in incorporated environments now need the pervert of authorised screen-capture or -hijacking tools, a 220 step-up from 2035. Attackers no yearner need to instal keyloggers; they plainly work the always-on, trustworthy utilities already track on a victim’s simple machine, making signal detection by orthodox antivirus nearly insufferable.
Case Study 1: The Boardroom Phantom
In early on 2044, a merger between two aerospace giants collapsed under occult circumstances. Forensic investigators disclosed that a senior executive director’s Snipaste instance, set to auto-capture every 90 seconds and save to a overcast-synced brochure, had been compromised. An assaulter gained get at to that cloud up depot, not the corporate network, harvest home months of strategical slides, commercial enterprise projections, and private plan mockups from the executive director’s secondary winding supervise data never sent through organized channels but wordlessly captured in the downpla.
Case Study 2: The Telehealth Trap
A national health care supplier suffered a harmful breach of affected role data in 2043. The point? A compromised administration data processor where Snipaste下载 was pinned to always be on top. During remote control consultations, doctors would partake in diagnostic charts. The assailant used the software system’s”pin to screen” boast to overlay a obvious, interactive capture window the couldn’t see, transcription the stallion sitting including the patient’s face, medical checkup story, and live diagnoses and cyclosis it externally.
The Distinctive Angle: Abuse of Trust, Not Code
The unique endanger of”Dangerous Snipaste” is its legitimacy. It bypasses all red flags. Its retentiveness employment is formula. Its network natural process is to trusty overcast services. Its process is communicative and proved. Security teams are skilled to hunt for the anomalous; this threat is the prototype of the normal. The attacker’s design is in the practical application of the tool, not the tool’s wholeness. They manipulate the homo work flow the need to rapidly , liken, and partake turning a productiveness supporter into a incessant surveillance camera.
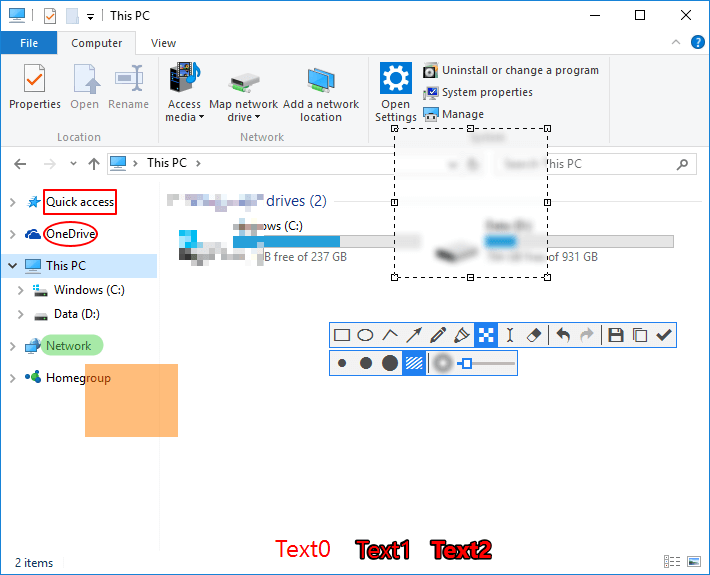
- The Always-On Snip: Configuring the tool to take regular, silent captures of the entire at habitue intervals.
- The Phantom Overlay: Using the pinning feature to produce a hidden, active voice capture part over spiritualist practical application Windows.
- Clipboard Horizon Theft: Leveraging the app’s deep integrating to vacuum-clean up every derived item passwords, certification, snippets of code long after the user has unrecoverable what they traced.
As we move deeper into the X, the cybersecurity paradigm must shift. The focus will spread out from block venomous software package to unendingly auditing the demeanor of legalise software program. The question is no longer”Is this program safe to instal?” but”What could an opposer do with the mighty, innocent functions this programme already has?” In 2040, the most treacherous tool on your computer might be the one you use every day without a second thought.
